The quiz in question. In case anyone is not familiar with it. (attractive?) prizes to be won.
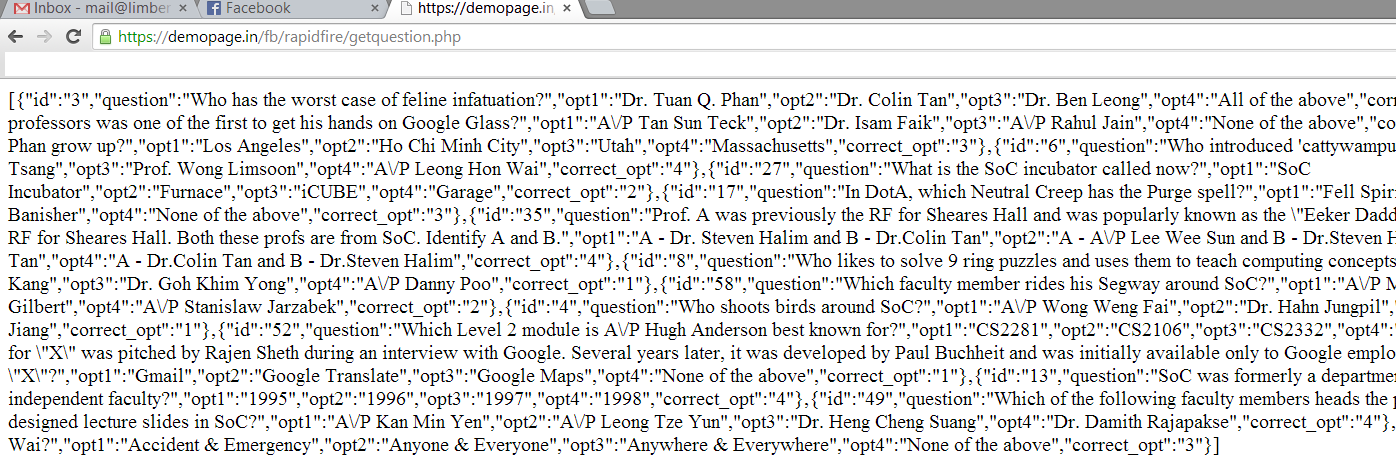
A quick packet capture revealed that the questions could be found here in JSON format. This is what is looked like. Interesting that the answers were included even through "marking" was done only on the server side. The questions were randomly generated.
The quiz allowed you to make repeated attempts to improve your score so the simplest way was to keep sending in your answers (automatically of course!). Since I was too lazy to parse the JSON and I figured that they probably didn't check for duplicate qns, I reused the same question number. The bash script.
#!/bin/bash
while :
do
curl -k -i --raw -o /dev/null -X POST -d "hiddenmemberid=(redacted)&redirecturl=https%%3A%%2F%%2Fwww.facebook.com%%2Fnusschoolofcomputing%%2F%%3Fsk%%3Dapp\_1441375262772058&token=3e191a89c94fda84460bfa8282d4d65a&radio0=1&qstnid0=4&radio1=1&qstnid1=4&radio2=1&qstnid2=4&radio3=1&qstnid3=4&radio4=1&qstnid4=4&radio5=1&qstnid5=4&radio6=1&qstnid6=4&radio7=1&qstnid7=4&radio8=1&qstnid8=4&radio9=1&qstnid9=4&radio10=1&qstnid10=4&radio11=1&qstnid11=4&radio12=1&qstnid12=4&radio13=1&qstnid13=4&radio14=1&qstnid14=4" "https://demopage.in/fb/rapidfire/resultfile.php" -H "Host: demopage.in" -H "Connection: keep-alive" -H "Cache-Control: max-age=0" -H "Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,\*/\*;q=0.8" -H "Origin: https://demopage.in" -H "User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/34.0.1847.131 Safari/537.36" -H "Content-Type: application/x-www-form-urlencoded" -H "Referer: https://demopage.in/fb/rapidfire/" -H "Accept-Encoding: gzip,deflate,sdch" -H "Accept-Language: en-US,en;q=0.8" -H "Cookie: PHPSESSID=(redacted)"
done
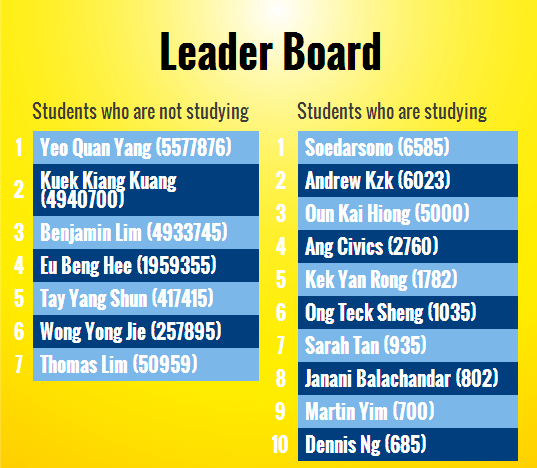
Obviously, I wasn't the only one to figure it out
The race to the end
To win, you couldn't send the packets 1 at a time. You needed to run multiple threads simultaneously. I had about 30 going on at the same time. My upload/download was about 50kb/120kb. Since the packet size was 500bytes, I was sending about 100 packets/second which is 7500 points/sec.
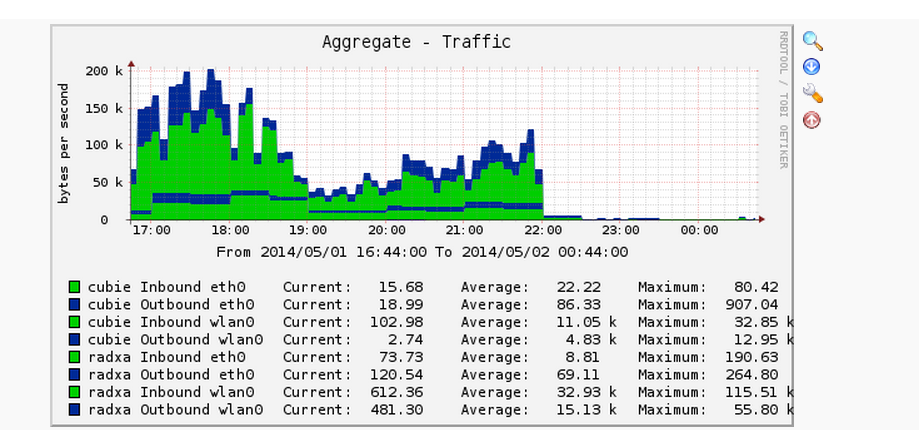
Except it wasn't really true. Turns out that my server at home is more powerful than theirs and it couldn't handle the load. This was not obvious to me at first. I always had the impression that DDOS/DOS was caused by bandwidth bottleneck. Attacks are measured in Gbps. Just google "ddos gbps". How could 50kbps possibly saturate their bandwidth? Although it is highly unscientific, I did check that I was the only one with points increasing at a rate which could be quantified in terms of points/sec. Since I was already in the lead by close to 20,000,000 points, I could afford to slow down and do a little experiment. I gradually decreased the rate at which I was sending packets until I hit what is supposedly the limit of the server at 7pm. I logged all responses received, slowing down the rate I was sending until the number of errors stabilised. Upload/download was about 12kb/40kb or 24 packets/sec.
while :
do
output=$(curl ....)
if ($output \| grep "200")
then echo "ok" >> access.log;
else
echo "err" >> error.log;
fi
done
Round 2
The quiz was modified midway in what I suppose was an attempt to thwart the use of scripts. It was a puzzling move as the makers of the quiz had already approved of the use of scripts, calling it the "soc way" and giving the 3rd prize to those who used scripts. Anyway, it did not really affect me. The change required a valid PHP session and so I manually completed the quiz once to obtain the session cookie which is used in future requests. The endpoint was also changed but a packet capture revealed the new endpoint.
Ethicality
By the time I found out about the quiz, the top 5 spots or so were already taken by scripters. Therefore, I wasn't depriving any legitimate player a chance at the prize, so I reasoned that it was ok. The DOS attack was unintentional, I had no idea that a single person with a 1mbps upload connection could DOS an entire instance and cause a number of websites to be unavailable. As for the prizes, I thought that I would be banned/blocked. After all, the main motivation was to destress and have fun.
The final results
